Alright, so we got a new SSL certificate and my theory does not appear to be correct. The clientssl parent profile has been changed to the clientssl-insecure-compatible
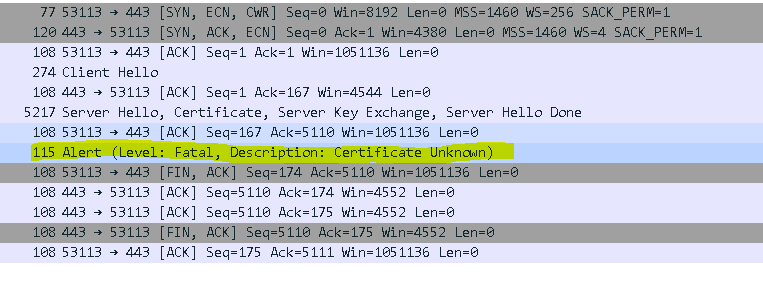
Here is a copy of the SSLDUMP:
New TCP connection 22: 192.168.105.92(59853) <-> 192.168.28.140(443)
22 1 0.0012 (0.0012) C>SV3.3(161) Handshake
ClientHello
Version 3.3
random[32]=
5b 8e d9 0f 64 f5 32 7b 1c 0b fc 92 41 a8 82 7e
cb f4 c2 0b 6a 7f f6 f9 30 0a f8 5c f6 85 17 bc
cipher suites
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
TLS_RSA_WITH_AES_128_CBC_SHA256
TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA256
TLS_ECDH_RSA_WITH_AES_128_CBC_SHA256
TLS_DHE_RSA_WITH_AES_128_CBC_SHA256
TLS_DHE_DSS_WITH_AES_128_CBC_SHA256
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
TLS_RSA_WITH_AES_128_CBC_SHA
TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA
TLS_ECDH_RSA_WITH_AES_128_CBC_SHA
TLS_DHE_RSA_WITH_AES_128_CBC_SHA
TLS_DHE_DSS_WITH_AES_128_CBC_SHA
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
TLS_RSA_WITH_AES_128_GCM_SHA256
TLS_ECDH_ECDSA_WITH_AES_128_GCM_SHA256
TLS_ECDH_RSA_WITH_AES_128_GCM_SHA256
TLS_DHE_RSA_WITH_AES_128_GCM_SHA256
TLS_DHE_DSS_WITH_AES_128_GCM_SHA256
TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA
TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
TLS_RSA_WITH_3DES_EDE_CBC_SHA
TLS_ECDH_ECDSA_WITH_3DES_EDE_CBC_SHA
TLS_ECDH_RSA_WITH_3DES_EDE_CBC_SHA
TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
TLS_DHE_DSS_WITH_3DES_EDE_CBC_SHA
TLS_EMPTY_RENEGOTIATION_INFO_SCSV
compression methods
NULL
22 2 0.0036 (0.0024) S>CV3.3(87) Handshake
ServerHello
Version 3.3
random[32]=
75 aa a3 00 16 c9 d3 98 56 56 25 51 f6 1c 62 bc
2b a1 99 ea 0b 79 9b d9 9b b8 df c8 86 e8 7c 24
session_id[32]=
aa 00 6c db 7f c5 60 3f 93 c9 50 e3 e6 0d 08 c7
34 e2 db 94 60 26 d7 30 42 be 6a a8 b6 9d 58 d7
cipherSuite TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
compressionMethod NULL
22 3 0.0036 (0.0000) S>CV3.3(4491) Handshake
Certificate
Subject
CN=itsdtest.example.com
Issuer
DC=com
DC=example
CN=InternalCA
Serial 5a 00 00 80 b0 f0 2d 42 8b 48 43 0b bf 00 01 00
00 80 b0
Extensions
Extension: X509v3 Key Usage
Extension: X509v3 Subject Key Identifier
Extension: X509v3 Subject Alternative Name
Extension: X509v3 Authority Key Identifier
Extension: X509v3 CRL Distribution Points
Extension: Authority Information Access
Extension: 1.3.6.1.4.1.311.21.7
Extension: X509v3 Extended Key Usage
Extension: 1.3.6.1.4.1.311.21.10
Subject
DC=com
DC=example
CN=InternalCA
Issuer
CN=InternalCAroot
Serial 44 00 00 00 03 5e eb 3e 5c 75 84 80 b2 00 00 00
00 00 03
Extensions
Extension: 1.3.6.1.4.1.311.21.1
Extension: 1.3.6.1.4.1.311.21.2
Extension: X509v3 Subject Key Identifier
Extension: 1.3.6.1.4.1.311.20.2
Extension: X509v3 Key Usage
Extension: X509v3 Basic Constraints
Critical
Extension: X509v3 Authority Key Identifier
Extension: X509v3 CRL Distribution Points
Extension: Authority Information Access
Subject
CN=InternalCAroot
Issuer
CN=InternalCAroot
Serial 1c 53 ec 09 e5 3f 49 ab 46 69 30 03 1c 2c eb 61
Extensions
Extension: X509v3 Key Usage
Extension: X509v3 Basic Constraints
Critical
Extension: X509v3 Subject Key Identifier
Extension: 1.3.6.1.4.1.311.21.1
22 4 0.0036 (0.0000) S>CV3.3(333) Handshake
ServerKeyExchange
22 5 0.0036 (0.0000) S>CV3.3(4) Handshake
ServerHelloDone
22 6 0.0042 (0.0006) C>SV3.3(2) Alert
level fatal
value certificate_unknown
22 0.0042 (0.0000) C>S TCP FIN
22 0.0043 (0.0000) S>C TCP FIN
 Altostratus
Altostratus Altostratus
Altostratus