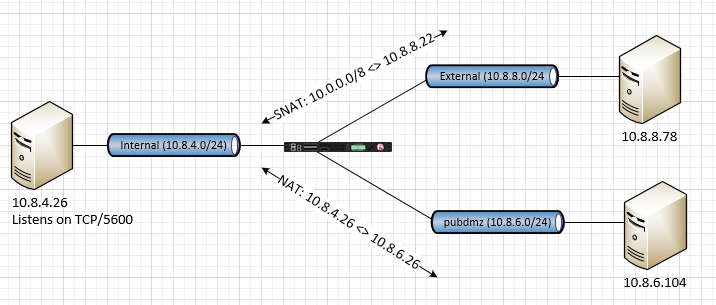
SNAT and NAT on difference vlans
 Nimbostratus
Nimbostratus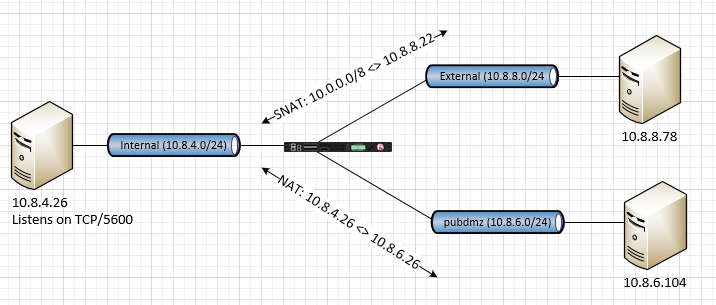
 Noctilucent
Noctilucentprobably you do not need irule. 🙂
e.g.
internal to external
ltm virtual internal-to-external {
destination 10.8.8.0:0
ip-forward
mask 255.255.255.0
profiles {
fastL4 { }
}
source 10.8.4.26/32
source-address-translation {
pool snat-10.8.8.22
type snat
}
translate-address disabled
translate-port disabled
vlans {
internal
}
vlans-enabled
vs-index 15
}
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm snatpool snat-10.8.8.22
ltm snatpool snat-10.8.8.22 {
members {
10.8.8.22
}
}
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm snat-translation 10.8.8.22
ltm snat-translation 10.8.8.22 {
address 10.8.8.22
inherited-traffic-group true
traffic-group traffic-group-1
}
internal to pubdmz
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm virtual internal-to-pubdmz
ltm virtual internal-to-pubdmz {
destination 10.8.6.0:0
ip-forward
mask 255.255.255.0
profiles {
fastL4 { }
}
source 10.8.4.26/32
source-address-translation {
pool snat-10.8.6.26
type snat
}
translate-address disabled
translate-port disabled
vlans {
internal
}
vlans-enabled
vs-index 16
}
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm snatpool snat-10.8.6.26
ltm snatpool snat-10.8.6.26 {
members {
10.8.6.26
}
}
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm snat-translation 10.8.6.26
ltm snat-translation 10.8.6.26 {
address 10.8.6.26
inherited-traffic-group true
traffic-group traffic-group-1
}
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm virtual pubdmz-to-internal
ltm virtual pubdmz-to-internal {
destination 10.8.6.26:0
mask 255.255.255.255
pool pool-10.8.4.26
profiles {
fastL4 { }
}
source 10.8.6.0/24
translate-port disabled
vlans {
pubdmz
}
vlans-enabled
vs-index 17
}
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm pool pool-10.8.4.26
ltm pool pool-10.8.4.26 {
members {
10.8.4.26:0 {
address 10.8.4.26
}
}
}
pubdmz to 10.8.4.26 on port 5600
root@(ve11a)(cfg-sync In Sync)(Active)(/Common)(tmos) list ltm virtual pubdmz-to-10.8.4.26
ltm virtual pubdmz-to-10.8.4.26 {
destination 10.8.4.26:5600
ip-forward
ip-protocol tcp
mask 255.255.255.255
profiles {
fastL4 { }
}
source 10.8.6.0/24
translate-address disabled
translate-port disabled
vlans {
pubdmz
}
vlans-enabled
vs-index 18
}
 Nimbostratus
Nimbostratus